By Robert Brzenchek, alumnus, Intelligence Studies at American Military University
Cyber threats from around the world are increasing in both scope and intensity. Recently, the first-ever National Cyber Security Summit was held in New York City where Department of Homeland Security (DHS) Secretary Kirstjen M. Nielsen summarized the state of our country’s cyber defenses:
“We are facing an urgent, evolving crisis in cyberspace. Our adversaries’ capabilities online are outpacing our stove-piped defenses. In fact, I believe that cyber threats collectively now exceed the danger of physical attacks against us. This is a major sea change for my department, and for our country’s security. Indeed, most Americans go about their daily lives without fear of personal injury or harm from our adversaries. But our digital lives are now in danger every single day.”
Gangs in nations like Russia or China can be particularly resourceful and dangerous – especially since governments there are secretly sponsoring hackers’ efforts and protecting them from international law enforcement, according to a former top FBI official.
[Related: Fighting Human Trafficking on Its Own Cyber-Turf]
“Both Russia and China are sponsoring hackers that collect information on behalf of the nation state. Intellectual property is being funneled to benefit companies in their home countries,” said Shawn Henry, former executive assistant director in charge of the FBI‘s Criminal, Cyber, Response and Services Branch.
Threats from Transnational Organized Crime Groups
Increasing threats are also coming from transnational organized crime groups (e.g., gangs and cartels). These influential organizations have lots of money and power, which means they have the ability to pay hackers to defeat cybersecurity measures.
“Mexican drug trafficking organizations are increasingly demonstrating a desire to make money from cybercrime, attracted by the high profits and minimal risks offered by such activities as fraud, theft, and piracy,” according to the Infosec Institute. The cartels are said to forcibly recruit computer programmers. If true, these groups are acquiring the skills and ability to reap the potential profits of cybercrime.
[Related: How Syrians are Using Cyber Community Policing to Fight Terrorism]
According to David Goldman of CNN Money, “Organized cybercrime is a truly an international affair, but the most advanced attacks tend to stem from Russia. The Russian mob is incredibly talented for a reason: After the Iron Curtain lifted in the 1990s, a number of ex-KGB cyberspies realized they could use their expert skills and training to make money off of the hacked information they had previously been retrieving for government espionage purposes.”
Measures to Improve Cybersecurity
The dangers posed by organized crime groups are nothing new. For decades, these organizations have launched sophisticated attacks against individuals as well as major corporations. Billions of dollars have been stolen every year, and large, continuous hacks of our highly sensitive computer systems.
What is new, is the acknowledgement that cybersecurity should be high priority for every individual, company, and government entity. Secretary Nielsen announced during the recent conference in NYC that DHS is helping facilitate this prioritization and providing support through the creation of the National Risk Management Center. This center will focus on implementing cybersecurity measures for financial services, telecommunications, and energy sectors. “The center will bring together government experts with willing industry partners so that they can influence how we support them. Our goal is to simplify the process, to provide a single point of access to the full range of government activities to defend against cyberthreats,” said DHS Secretary Nielsen during the National Cyber Security Summit.
While DHS’s involvement in cybersecurity is a step in the right direction, more measures need to be put in place that facilitates collaboration across industries and government entities. For example, to measure the nation’s cybersecurity efforts there needs to be a diverse membership comprised of federal and state regulators with responsibility for oversight of publicly/privately owned facilities, privately owned and operated suppliers, crisis-level and regional management authorities, and other parties.
The membership should be familiar with the International Standards Organization (ISO) standards, and in every case, experienced with implementation and auditing organizations and facilities that have chosen to adopt voluntary, standards-based management systems.
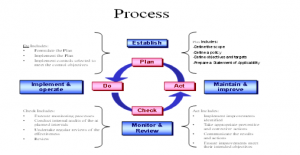
This membership should have interests conforming to the voluntary frameworks exemplified in the Plan-Do-Check-Act models common to quality, environmental, health, safety and security standards of the ISO.
It will take both the private and public sector’s best and brightest to collaborate and address the increasing cybersecurity threats. The threats are only going to increase and the nation’s public and private entities must band together to combat this evolving threat to our nation’s security.
About the Author: Robert M. Brzenchek is a consultant, subject matter expert, and expert witness in the criminal justice and emergency management arenas. He has extensive cybersecurity experience as the current HLS/Cyber Chair for Strengthening the Mid-Atlantic Region (SMART); a member of the Spectrum Group Security Team consulting on ISO (27001, 28000) projects globally; a former member of the ASIS Investigative Standards Technical Committee; and conducted ISO 27001 internal audits since 2005. He earned a master’s degree in intelligence studies from American Military University and is currently a Ph.D. candidate at Capella University with a proposed dissertation focused on gangs. He was a police officer for six years, where he performed suppression and intervention techniques with various gangs ranging from MS-13, Bloods, Crips, and Latin Kings. In the private sector since 2005, he has worked with DHS, DOD, large corporations, ports, and public utilities on security matters, risk management, policy, and technologies. He is a nationally certified instructor with the International Association of Directors of Law Enforcement Standards and Training (IADLEST). To contact him, email IPSauthor@apus.edu. For more articles featuring insight from industry experts, subscribe to In Public Safety’s bi-monthly newsletter.

Comments are closed.